Multiple tokens were involved in the transfer. According to sources, investigators suspect the Lazarus Group — a North Korea–linked hacking organization — is behind the attack. This suspicion is based on strong similarities to the 2019 Upbit breach, during which 342,000 ETH were stolen.
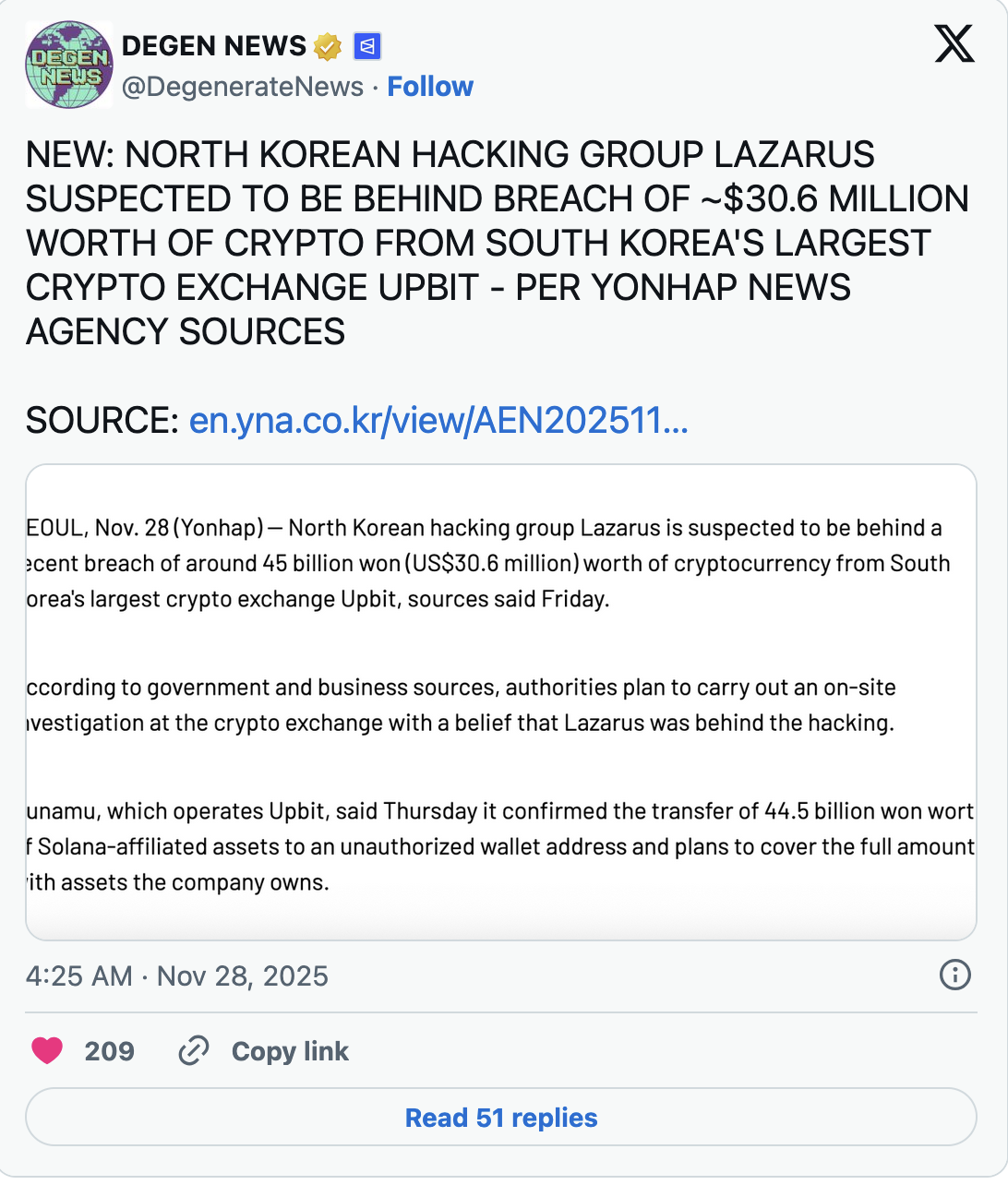
Upbit’s operator, Dunamu, has pledged to fully compensate the losses using its own assets. An on-site inspection is also expected to take place in the coming days.
Signs of the Same Playbook
The attack method closely mirrors the 2019 breach, in which assets worth approximately 58 billion won were stolen. In that case, the funds were laundered through multiple crypto exchanges — a tactic commonly associated with North Korean cybercriminal groups. Law enforcement sources describe the pattern as a clear “Lazarus signature.”
The National Police Agency’s cybercrime unit is leading the investigation. No further technical details have been disclosed at this stage. The country’s intelligence service has also declined to comment.
Shift Toward Social Engineering
According to cybersecurity experts, the Lazarus Group has increasingly moved away from complex malware and software vulnerabilities in recent years. Instead, it relies more heavily on social engineering — stealing credentials, impersonating employees, and gaining internal access to systems.
A similar tactic was used in the February 2025 attack on Bybit, where approximately $1.5 billion was stolen through phishing-based methods. Upbit’s scale and high liquidity made it an attractive target for organized cyber groups seeking rapid access to liquid digital assets. Investigators have not ruled out the possibility that an administrator-level account was compromised, further strengthening the theory that human factors — not technical flaws — were the main entry point.
Rising Risk for the Crypto Industry
If Lazarus involvement is confirmed, it will align with North Korea’s broader strategy of acquiring digital assets through cybercrime. In the past, the U.S. FBI has described such groups as “advanced persistent threats.”
Experts emphasize that the highest risk today lies not only in wallets and smart contracts, but in employee access systems — especially those with administrative privileges. Exchanges are being pushed to strengthen identity verification, internal procedures, and access control protocols. Increased coordination between regulators and law enforcement is also expected, including wallet tracking, cross-border data sharing, and enhanced transaction analysis.
This case raises an important question: can crypto exchanges, built on open finance principles, effectively defend themselves against state-sponsored cyber operations based not on code exploitation, but on identity compromise?

